FRAUDULENT ACCOUNT DETECTION IN THE ETHEREUM’S NETWORK USING VARIOUS MACHINE LEARNING TECHNIQUES
DOI:
https://doi.org/10.15282/ijsecs.8.2.2022.5.0102Keywords:
Ethereum; Fraudulent Accounts ; Machine LearningAbstract
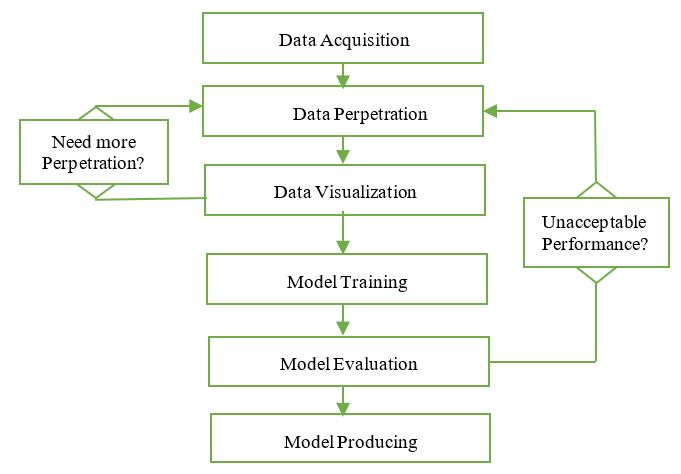
On the Ethereum network, users communicate with one another through a variety of different accounts. Pseudo-anonymity was enforced over the network to provide the highest level of privacy. By using accounts that engage in fraudulent activity across the network, such privacy may be exploited. Like other cryptocurrencies, Ethereum blockchain may exploited with several fraudulent activities such as Ponzi schemes, phishing, or Initial Coin Offering (ICO) exits, etc. However, the identification of parameters with abnormal account characteristics is not an easy task and requires an intelligent approach to distinguish between normal and fraudulent activities. Therefore, this paper has attempted to solve this a problem by using machine learning techniques to introduce a robust approach that can detect fraudulent accounts on Ethereum. We have used a K-Nearest Neighbor, Random Forest and XGBoost over a collected dataset of 4,681 instances along with 2,179 fraudulent accounts associated and 2,502 regular accounts. The XGBoost, RF, and KNN techniques achieved average accuracies of 96.80 %, 94.8 8%, and 87.85% and an average AUC of 0.995, 0.99 and 0.93, respectively.
Downloads
References
Sapra, Riya, and Parneeta Dhaliwal. "Blockchain: the new era of technology." In 2018 fifth international conference on
parallel, distributed and grid computing (PDGC), pp. 495-499. IEEE, 2018.
Nakamoto, Satoshi. "Bitcoin: A peer-to-peer electronic cash system." Decentralized Business Review (2008): 21260.
Ahram, Tareq, Arman Sargolzaei, Saman Sargolzaei, Jeff Daniels, and Ben Amaba. "Blockchain technology innovations."
In 2017 IEEE technology & engineering management conference (TEMSCON), pp. 137-141. IEEE, 2017.
Ekblaw, Ariel, Asaph Azaria, John D. Halamka, and Andrew Lippman. "A Case Study for Blockchain in Healthcare:“MedRec”
prototype for electronic health records and medical research data." In Proceedings of IEEE open & big data conference, vol.
, p. 13. 2016.
Yavuz, Emre, Ali Kaan Koç, Umut Can Çabuk, and Gökhan Dalkılıç. "Towards secure e-voting using ethereum blockchain."
In 2018 6th International Symposium on Digital Forensic and Security (ISDFS), pp. 1-7. IEEE, 2018.
Massimo FLORE, How Blockchain-Based Technology Is Disrupting Migrants' Remittances: A Preliminary Assessment, EUR
EN, Publications Office of the European Union, Luxembourg, 2018.
Jamil, Faisal, Omar Cheikhrouhou, Harun Jamil, Anis Koubaa, Abdelouahid Derhab, and Mohamed Amine Ferrag.
"PetroBlock: A blockchain-based payment mechanism for fueling smart vehicles." Applied Sciences 11, no. 7 (2021): 3055.
Pranav Ratta, Amanpreet Kaur, Sparsh Sharma, Mohammad Shabaz, Gaurav Dhiman, "Application of Blockchain and Internet
of Things in Healthcare and Medical Sector: Applications, Challenges, and Future Perspectives", Journal of Food
Quality, vol. 2021, Article ID 7608296, 20 pages, 2021
Kar, Arpan Kumar, and L. Navin. "Diffusion of blockchain in insurance industry: An analysis through the review of academic
and trade literature." Telematics and Informatics 58 (2021): 101532.
Guo, J., Li, C., Zhang, G. et al. Blockchain-enabled digital rights management for multimedia resources of online
education. Multimed Tools Appl 79, 9735–9755 (2020)
Guustaaf, Edward, Untung Rahardja, Qurotul Aini, Herliana Wahyu Maharani, and Nesti Anggraini Santoso. "Blockchainbased Education Project." Aptisi Transactions on Management (ATM) 5, no. 1 (2021): 46-61.
Adams, R, Parry, G, Godsiff, P, Ward, P. The future of money and further applications of the blockchain. Strategic
Change. 2017; 26: 417– 422.
Christian Catalini and Joshua S. Gans. 2020. "Some simple economics of the blockchain," Communication of the ACM 63, 7
(July 2020), 80–90.
Li, Xiaoyun, Zibin Zheng, and Hong-Ning Dai. "When services computing meets blockchain: Challenges and opportunities."
Journal of Parallel and Distributed Computing 150 (2021): 1-14.
Lim, Ming K., Yan Li, Chao Wang, and Ming-Lang Tseng. "A literature review of blockchain technology applications in
supply chains: A comprehensive analysis of themes, methodologies and industries." Computers & Industrial Engineering 154
(2021): 107133.
Farrugia, Steven, Joshua Ellul, and George Azzopardi. "Detection of illicit accounts over the Ethereum blockchain." Expert
Systems with Applications 150 (2020): 113318.
European Parliament, Directorate-General for Internal Policies of the Union, Snyers, A., Houben, R.
(2018). Cryptocurrencies and blockchain : legal context and implications for financial crime, money laundering and tax
evasion, European Parliament.
Valenta, Martin, and Philipp Sandner. "Comparison of ethereum, hyperledger fabric and corda." Frankfurt School
Blockchain Center 8 (2017): 1-8.
Buterin, Vitalik. "A next-generation smart contract and decentralized application platform." white paper 3, no. 37 (2014).
Wood, Gavin. "Ethereum: A secure decentralised generalised transaction ledger." Ethereum project yellow paper 151, no.
(2014): 1-32.
Vujičić, Dejan, Dijana Jagodić, and Siniša Ranđić. "Blockchain technology, bitcoin, and Ethereum: A brief overview."
In 2018 17th international symposium infoteh-jahorina (infoteh), pp. 1-6. IEEE, 2018
Dannen, Chris. Introducing Ethereum and solidity. Vol. 1. Berkeley: Apress, 2017.
Wang, Shuai, Liwei Ouyang, Yong Yuan, Xiaochun Ni, Xuan Han, and Fei-Yue Wang. "Blockchain-enabled smart contracts:
architecture, applications, and future trends." IEEE Transactions on Systems, Man, and Cybernetics: Systems 49, no. 11
(2019): 2266-2277
Carlin, Domhnall, Philip O’kane, Sakir Sezer, and Jonah Burgess. "Detecting cryptomining using dynamic analysis." In 2018
th Annual Conference on Privacy, Security and Trust (PST), pp. 1-6. IEEE, 2018.
Chen, Weili, Zibin Zheng, Jiahui Cui, Edith Ngai, Peilin Zheng, and Yuren Zhou. "Detecting ponzi schemes on ethereum:
Towards healthier blockchain technology." In Proceedings of the 2018 world wide web conference, pp. 1409-1418. 2018.
Jung, Eunjin, Marion Le Tilly, Ashish Gehani, and Yunjie Ge. "Data mining-based ethereum fraud detection." In 2019 IEEE
International Conference on Blockchain (Blockchain), pp. 266-273. IEEE, 2019
Baek, Hyochang, Junhyoung Oh, Chang Yeon Kim, and Kyungho Lee. "A model for detecting cryptocurrency transactions
with discernible purpose." In 2019 Eleventh International Conference on Ubiquitous and Future Networks (ICUFN), pp.
-717. IEEE, 2019
Poursafaei, Farimah, Ghaith Bany Hamad, and Zeljko Zilic. "Detecting Malicious Ethereum Entities via Application of
Machine Learning Classification." In 2020 2nd Conference on Blockchain Research & Applications for Innovative Networks
and Services (BRAINS), pp. 120-127. IEEE, 2020
Chen, Weili, Xiongfeng Guo, Zhiguang Chen, Zibin Zheng, and Yutong Lu. "Phishing Scam Detection on Ethereum:
Towards Financial Security for Blockchain Ecosystem." In IJCAI, pp. 4506-4512. 2020
Wang, Lei, Hao Cheng, Zibin Zheng, Aijun Yang, and Xiaohu Zhu. "Ponzi scheme detection via oversampling-based Long
Short-Term Memory for smart contracts." Knowledge-Based Systems 228 (2021): 107312
Hu, Huiwen, Qianlan Bai, and Yuedong Xu. "Scsguard: Deep scam detection for ethereum smart contracts." In IEEE
INFOCOM 2022-IEEE Conference on Computer Communications Workshops (INFOCOM WKSHPS), pp. 1-6. IEEE, 2022.
Van der Maaten, Laurens, and Geoffrey Hinton. "Visualizing data using t-SNE." Journal of machine learning research 9,
no. 11 (2008).
Chen, Tianqi, and Carlos Guestrin. "Xgboost: A scalable tree boosting system." In Proceedings of the 22nd acm sigkdd
international conference on knowledge discovery and data mining, pp. 785-794. 2016
Bentéjac, Candice, Anna Csörgő, and Gonzalo Martínez-Muñoz. "A comparative analysis of gradient boosting
algorithms." Artificial Intelligence Review 54, no. 3 (2021): 1937-1967
Breiman, Leo. "Random forests." Machine learning 45, no. 1 (2001): 5-32.
Hand, David J. "Principles of data mining." Drug safety 30, no. 7 (2007): 621-622.
Müller, Andreas C., and Sarah Guido. Introduction to machine learning with Python: a guide for data scientists. " O'Reilly
Media, Inc.", 2016.
Géron, Aurélien. Hands-on machine learning with Scikit-Learn, Keras, and TensorFlow: Concepts, tools, and techniques to
build intelligent systems. " O'Reilly Media, Inc.", 2019.
Downloads
Published
Issue
Section
License
Copyright (c) 2022 Amer Sallam, Taha Rassem, Hanadi Abdu, Haneen Abdulkareem, Nada Saif, Samia Abdullah

This work is licensed under a Creative Commons Attribution-NonCommercial 4.0 International License.